Wipe the Drive Dude! Techniques for Malware Persistence
Jake Williams: Hi! I’m Jake Williams. I’m a Principal Forensic Analyst for CSRgroup; I’m a SANS Forensics 610 Instructor – that’s, not surprisingly, malware. I’m doing research right now on cloud forensics, and I like to break poorly written software because…who doesn’t?

Jake Williams
◦ CSRgroup – Principal Forensic Analyst
◦ SANS FOR610 Instructor
◦ Cloud forensics researcher
◦ Breaker of poorly written software
Mark Baggett: My name is Mark Bagget. I’m also a SANS pentester, SANS instructor for the pentest curriculum; handler for the Internet Storm Center; blogger for PaulDotCom; and I’m course author for a new SANS penetration testing course where we’re going to be using Python. It’s in beta, and the beta is going to be running in 30 days here in town; it’s 50% off. If you want some more information, see the SANS booth.

Mark Baggett
◦ SANS instructor – SEC573 Python Course Author
◦ Internet Storm Center Handler
◦ Blogger for Pauldotcom, SANS Pentest Blog
◦ Security Certification connoisseur
Jake Williams: That’s not a bad course. I went through some of the beta stuff with Mark – good stuff.
Mark Baggett: So, today we’re here to talk about Wipe the Drive. What we’re saying is, if you have malware on your machine, then without question the best course of action is to just wipe the drive, not depend upon forensics or software to clean up that malware on your behalf. Forget it – wipe the drive. And the reason we feel like we need to say this is because there is this bias against just wiping the drive, for example from technicians – you’ll hear technicians say things like: “I think that people who wipe the drive just want to wipe the drive and not take on the task of removing that malware; they just lack the intestinal fortitude to take on the challenge of wiping the drive. Or you’ll hear from the business things like: “You’re the security guy! I pay you to know how to remove malware from my systems. Why are you coming in here telling me to wipe the drive on these systems?”
WHY WE NEED TO SAY IT?
Overheard from PC Technicians
◦ “I think that technicians who wipe the drive instead of removing the virus are wimps.”
◦ “Malwarebytes will find and remove anything.”
◦ “I hate people who are too stupid to remove viruses and insist on wiping the drive”
From the business
◦ “We don’t have time to wait for you to reinstall all that software.”
◦ “Don’t I pay you to know how to remove viruses?
◦ “Thanks. You found the malware. Our IT team will take it from here.”
But what we want to do here today is to put together some techniques that are going to demonstrate that what malware or attackers who have been on your systems as a result of malware infection can do is modify the configurations on your system or leave things behind that will not be detected by antivirus software. The antivirus software isn’t even looking for it. And that is going to leave some unique configuration on the machine that will allow the attacker at some point in the future to either trigger an event that will cause the re-infection of the machine, or know that some event is scheduled to happen that they can take advantage of that will cause the re-infection of that machine.
Jake Williams: And so we want to be honest. As a consultant who gets paid by the hour, I prefer that you don’t wipe the drive. That means, don’t take my advice, I like repeat engagements – again, I’ll get paid by the hour.
So, what are we doing here? Well, this really came out of some of the incidents that I’ve worked on over the last 1-1.5 years here, and some experience of Mark as well on the incident handling side; and then sitting together and brainstorming. So we’re going to present 8 techniques today. We don’t think we’ve got them all covered. In fact, we’re positive we don’t have them all covered. We want to start a repository for these things, and that’s where wipethedrive.com comes in. So we’re going to put detailed implementations of these techniques on the website sometime this weekend.
HOW WE ARE GOING TO SAY IT?
◦ A new central repository for stealthy persistence techniques
◦ Details on the implementation of these techniques will be on the website
◦ This presentation is intended to kick off thecreative process with a few interesting techniques
This presentation is really intended to kick off and basically start the conversation. We’re going to present some techniques; hopefully you can use them from a pentesting standpoint or from, certainly, incident response standpoint – things you should be looking for. But again, certainly, we’re looking to start a good conversation about this; if you have techniques – definitely we’re all ears.
Mark Baggett: The details of what we are going to be talking about today will be included in a longer presentation that will be posted on the website as well.
The techniques that we’re looking at are creative ways that you can trigger the re-infection of a machine. These are techniques that can be used after the incident response has occurred. So, they knew viruses or some type of malware was on the system; the incident responders come in, they clean the system by running antivirus software, not by wiping the drive; they do their memory forensics and they find nothing in the memory. And at some point later in time, preferably being triggered by the attacker remotely, the re-infection occurs.
CRITERIA FOR THESE TECHNIQUES
◦ Nothing malicious is running in memory forobvious detection with memory forensics
◦ Starts itself via an interesting method – No HKLM\Software\Microsoft\Windows\CurrentVersion\Run
◦ Ideally triggered by attacker on demand
◦ All techniques are triggered based upon some action that occurs after incident response process has concluded
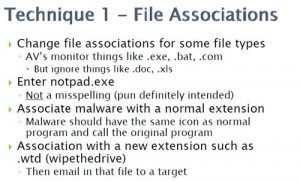
Jake Williams: The first technique we’re going to talk about is file associations. Antiviruses have been all over this for years – the .exe, the .com, the .bat. Basically, the file associations handle how the shell knows which program will be used to open up a file when you double-click on it. They do ignore things like .doc and .xls, because maybe you want to install Microsoft Office, or maybe for some reason you prefer OpenOffice and you’d rather use that, right? But they don’t monitor those; you have to be able to change those. And so, this one actually came from a compromise that we ran, and we went in, cleaned the malware off, I got a good repeat engagement off of it – I love repeat engagements; they would not take the server offline. And notpad.exe turned out to be the re-infection vector. So, basically we cleaned the malware off, this was just that the production server couldn’t be take down, definitely we couldn’t afford the business loss; and basically the attacker had replaced the file association for .log and .text on the server. And so, at some later point in time – 2 or 3 weeks later – the admin is on the box, opens up a .log file in notpad.exe, which kicks off notepad.exe and also re-infects the machine.
So, again, we just associate malware with some normal extension, or we can get a little bit more creative with it – we can create a new extension, something like .wtd, ‘wipe the drive’; and then we can email a file to the admin with that extension. The admin double-clicks on it. What gets the chance to handle the file? The malware. So we do think that file associations are going to be a good technique for secondary persistence; we’ve already seen it used in at least one attack.
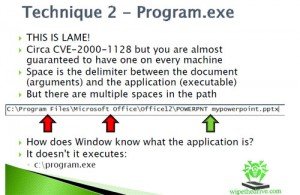
Mark Baggett: This one is lame.
Jake Williams: We weren’t going to have this one on the presentation originally. This was not in the original list.
Mark Baggett: I lobbied against it. I thought we were going to be booed off the stage. BUT…So I did this post on the Internet Storm Center that talked about this technique, and what I got was email after email streaming in from people talking about these different applications that they found on their systems, that are exploitable via this vulnerability. And I’m convinced that just about every Windows system that exists today has at least one of these particular vulnerabilities that will allow you to re-infect.
So, what is the vulnerability? First off, it’s been around since 2000. We shouldn’t be dealing with this today, but sadly, we still are on every single machine. As you take a path like this: C:\Program Files\Microsoft Office\Office12\POWERPNT mypowerpoint.pptx – how does the operating system know the difference between the document you want to open and the executable? It’s based upon the spaces, spaces are delimiters. But there’re spaces in my path, so how does it know that I don’t want to launch the C:\program.exe, or C:\Program Files\Microsoft.exe? How does it know that I want to launch POWERPNT.exe? And the answer is – it doesn’t! It tries them all. First thing it tries to load is C:\program.exe; then it moves down the chain until it gets it right. So you drop your malware on the hard drive under C:\program.exe, and on any machine today you are just about guaranteed that it’s going to be launched at some point in time by applications like Microsoft Defender, Java, Adobe, Flash, PowerPoint, etc. All these applications are launching program.exe. You can test this by taking a copy of calculator, putting it on your hard drive as program.exe – and just watch all the calcs that launch on your machine or launch in the background invisibly.
This site is just gret. I’ve looked these stuffs a whole lot and I view it that is good
written, fast to understand. I congratulate you for this article that I am going
to recommend to people friends. I ask you to visit the
gpa-calculator.co site where each learner or university student
can find results grade point average marks. All good!