Remove DNS Keeper malware and ads in Chrome, Firefox and IE
Ads by DNS-Keeper begin to fill up web pages on a PC that got attacked by a piece of adware, therefore they won’t vanish unless a removal procedure is applied.
The light-fingered publisher of DNS Keeper software is using a smart marketing catch to reach some clearly malefic goals. The app is stated to provide access to restricted online media for free, which is a feature that would certainly come in handy to a great many users. This potential demand is chiefly caused by the much talked-of trend where popular services like Crackle, Netflix and HBO are leveraging the blacklisting of ISPs that operate in some locations across the globe. According to the product review published by its makers on vidpot.tv, the geolocation factor won’t matter if the software is installed and launched. The trick, allegedly, is to proxy a certain part of user data in order to make it look like the traffic is originating at a different spot. The officially declared mission of DNS Keeper version 1.3 and version 1.4 and the actual output of its activity, regretfully, aren’t even close to a match. It serves numerous advertisements by embedding them into the pages visited during one’s web surfing.
The ad-injection problems usually begin to manifest themselves after the user installs an affiliated open source program. The list of such accomplices is versatile as it includes tens of products that are absolutely harmless by themselves. In the meantime, the criminals are taking advantage of bundled installations, where the setup of legit apps like Ashampoo Snap 8.0 Full Crack, Norton solutions and many others is complemented with one or a few additional offers, DNS Keeper being amongst those. As soon as this intrusion is allowed by the unsuspecting person, the infection instantly modifies the Local Area Connection settings on the system. This isn’t primarily done for virtual private networking purposes – instead, the objective is to gain sufficient control on the machine so as to display ads.
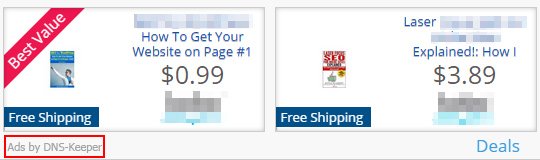
The malware adds a scheduled task so that its executable is started every time the PC is booted up. A couple of known variants of this malicious process are dnsdaisetta.exe, dnstolley.exe, and dnsridgewood.exe. As long as one of these is running, the victim’s Internet browsing is a bugging experience of extra ads flooding web pages all the time. The virus displays deals, discounts and coupons inside boxes that emerge in random places across sites. Some strings of text will turn blue and clickable, with further popups showing up as the cursor moves towards them. Multiple interstitial windows are going to pester the user as well.
In the event Ads by DNS-Keeper are encountered in the browser, adware removal should be urgently carried out. The unwanted code will not disappear unless ad hoc measures are adopted, so stick with the steps below to undo the harm and get rid of all the corrupt components.
DNS Keeper removal with automatic cleanup tool
An optimal workflow for eliminating the DNS Keeper adware is to leverage a security application which will identify all potentially malicious software on your computer and handle it the right way. This approach ensures thoroughness of the removal and system remediation, and allows avoiding unintended damage that might occur as a result of manual malware deletion.
1. Download and install DNS Keeper removal software. Launch it and click the Start New Scan button. Wait for the application to check your computer for threats

Download Ads by DNS-Keeper remover
2. When the app is done scanning your system, it will come up with an extensive list of detected objects. Click the Fix Threats option to have the utility completely remove this adware and affiliated infections found on your PC.
Uninstall troublemaking software through Control Panel

– Go to Start menu and select Control Panel on the list

– Click on the Add or Remove Programs (Uninstall a program) button
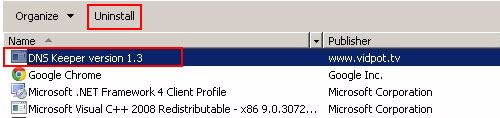
– Take a good look at the software list displayed. Search for DNS Keeper (version 1.3 and version 1.4) or other questionable items that look like they are ecommerce-related. When found, the culprit should be uninstalled
– Be advised DNS Keeper should but may not necessarily be listed anywhere on Control Panel therefore it may be problematic to figure out which particular program is associated with the virus in your case. If you are unsure, stick to the automatic cleanup advice or try the browser reset option described below.
Restore original Local Area Connection settings
Part of the unacceptable effect of DNS Keeper is the distortion of LAN properties. A full fix, therefore, implies reverting this component to its normal state.

– Open up Control Panel and select View network status and tasks under Network and Internet entry
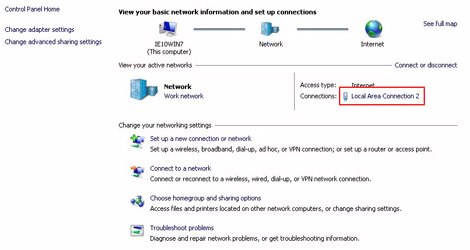
– Proceed to Local Area Connection as shown below
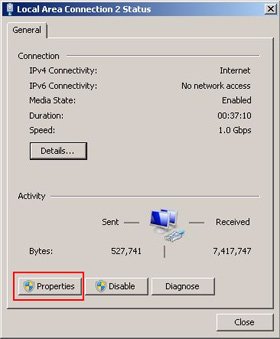
– Click Properties on the status dialog
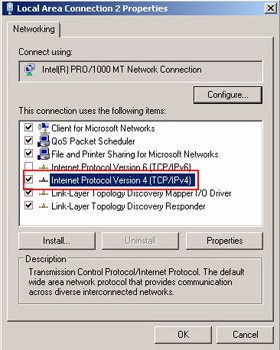
– Click the Internet Protocol Version 4 (TCP/IPv4) entry and select Properties
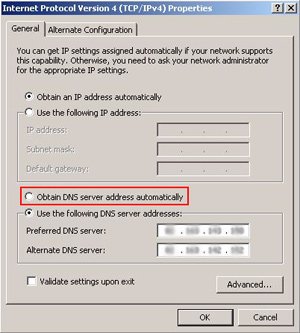
– Select the option to obtain DNS server address automatically and click OK to save the changes
Get rid of DNS-Keeper Ads by resetting the affected browser
FYI: This procedure will lead to the loss of custom browser settings, including bookmarks, cookies, passwords saved, and all browsing history. Also, some components of the virus may be beyond the browsers proper. Please keep this in mind when making a decision to proceed.
Reset Internet Explorer to its defaults
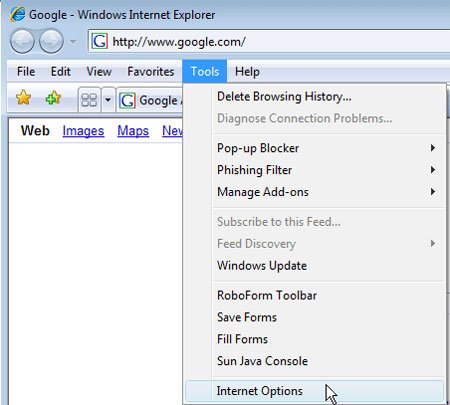
– Go to Tools –> Internet Options
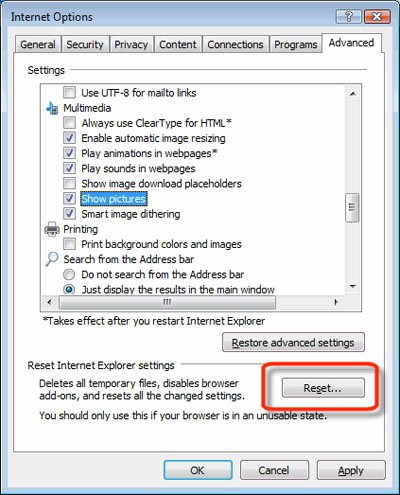
– Select the Advanced tab as shown below and click the Reset button
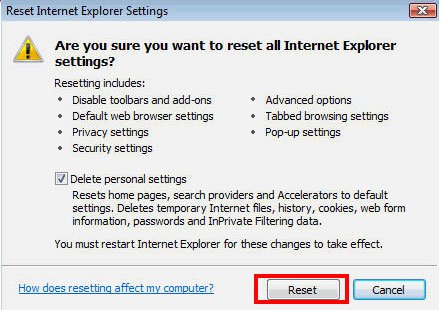
– Read the warning about the effects of resetting IE. If you are sure, proceed by checking the Delete personal settings option and clicking Reset
Reset Mozilla Firefox
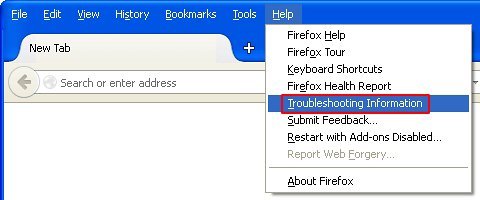
– Go to Help –> Troubleshooting Information
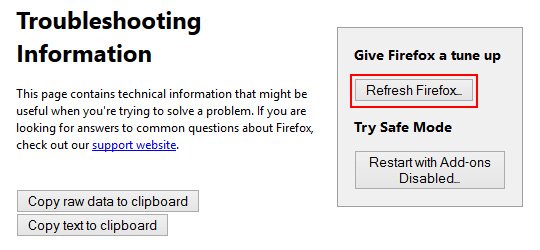
– Firefox will come up with the Troubleshooting Information screen. Click the Refresh Firefox button to complete the process
Reset Google Chrome
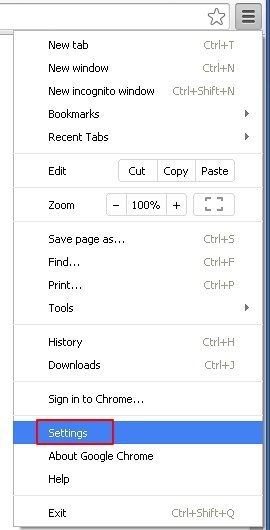
– Go to the Chrome Menu icon and pick Settings on the list
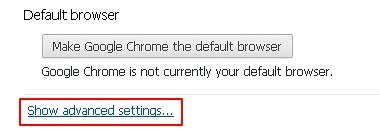
– Click on the Show advanced settings button

– Click on the button reading Reset browser settings
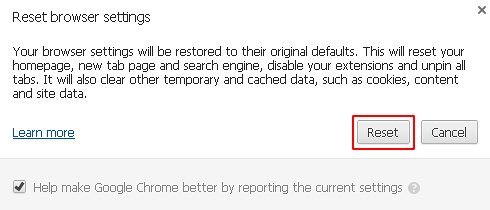
– On the notification box that pops up, review the consequences of Chrome reset and click Reset if it’s ok with you
Double-checking never hurts
To make sure the DNS Keeper adware has been removed, consider running an additional security scan as a completion of the cleanup procedure.

Download and install DNS Keeper removal software
Leave a Reply